Prior Work
The earliest mention of shims relating to security was in 2007 when a software engineer named Alex Ionescu started to publish a number of blog posts titled, ‘Secrets of the Application Compatilibity Database (SDB)’. This was planned to be a 7 part series but unfortunately Ionescu stopped after the fourth post. In the years preceding and following, a small number of disparate bloggers posted various technical details and mentions of shims, but typically with the focus of application compatibility. Below is a general timeline of major shim references:
- June 2005. A Microsoft Employee named Chris Jackson’s started an MSDN blog called, ‘The App Compat Guy’. Around January 2007 he began posting information about the ACT and blogging about shims. http://blogs.msdn.com/b/cjacks/
- May 2007. Ionescu ‘Secrets of the Application Compatilibity Database (SDB)’ www.alex-ionescu.com/?p=39
- August 2008. A blogger with the handle ‘wedday’ posted some technical details about how the shim engine worked based on the shim engine’s debug output. http://wedday.blogspot.co.uk/2008/08/shimeng.html
- July 2009. Another Microsoft Employee named ‘Maarten van de Bospoort’ wrote a blog post titled ‘Disabling a Shim’. However his solution was to disable the shim engine via group policy which is not advised because Windows relies on the shim engine for EMET and Fixit patches (discussed later). (Bospoort, 2009) http://blogs.msdn.com/b/maartenb/archive/2009/07/24/disabling-a-shim.aspx
- February 2010. A developer who goes by the name, ‘Jochen Kalmbach’ posted a tool that will display the shims that would be activated by a particular file. http://blog.kalmbach-software.de/2010/02/22/the-shim-database/
- April 2012. A company named ‘Recx’ posted a compilation of research notes titled ‘Windows AppCompat Research Notes’ where deep technical insight and control flow of the shim engine was discussed. (Ollie, 2012) http://recxltd.blogspot.co.uk/2012/04/windows-appcompat-research-notes-part-1.html
- May 2012. Microsoft updated its Application Compatibility Toolkit (ACT) Technical Reference where background information is given on the ACT along with details of individual fixes. This article also links to the AppHelp.dll documentation. https://technet.microsoft.com/en-us/library/hh825181.aspx
- October 2013. Mark Baggett gave a talk at DerbyCon titled, ‘Windows – Own3d by Default’. He is the first to discuss the use of shims in a post exploitation context. http://www.irongeek.com/i.php?page=videos/derbycon3/4206-windows-0wn3d-by-default-mark-baggett
- March 2014. Jon Erickson presented at Black Hat Asia ‘Persist-It – Using and Abusing Microsoft Fix It Patches’ where he describes how Fixit patches work and how his tool can be used to analyze them. (Erickson, 2014) https://www.blackhat.com/docs/asia-14/materials/Erickson/Asia-14-Erickson-Persist-It-Using-And-Abusing-Microsofts-Fix-It-Patches.pdf https://www.blackhat.com/docs/asia-14/materials/Erickson/WP-Asia-14-Erickson-Persist-It-Using-And-Abusing-Microsofts-Fix-It-Patches.pdf
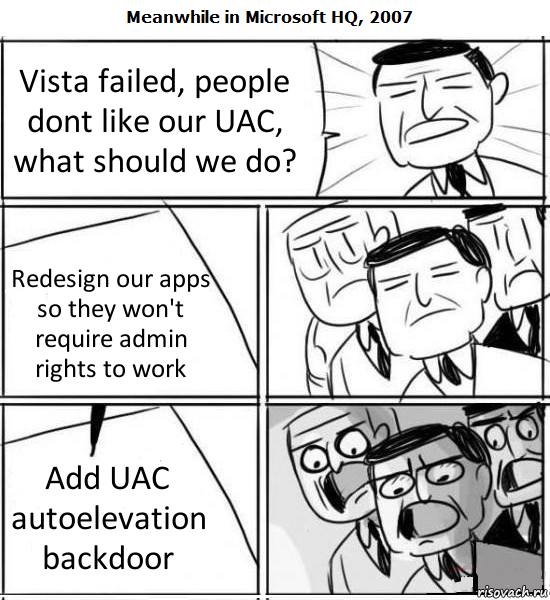
- May 2014. Graham Posts ‘Shimming your Way Past UAC’ (Graham, 2014). This provided the first public source code reference for how the ACT can be used to bypass a UAC prompt. http://blog.ddifrontline.com/4#more-4
- December 2014. Jon Erickson presents ‘The active use and exploitation of Microsoft's Application Compatibility Framework’ at SysScan 360 and CodeBlue in Japan. http://sdb.io/erickson-codeblue.pdf
- Jan 2015. Sean Pierce (me) Shmoocon Epilogue “Forensic Analysis of Advanced Persistence through the Application Compatibility Toolkit”
Paper Bibliography
- Aquilino, B. (2014, 6 30). Beware BlackEnergy If Involved In Europe/Ukraine Diplomacy. Retrieved from F-Secure: https://www.f-secure.com/weblog/archives/00002721.html
- Author. (2015, 2 8). Upatre downloader malware using AppCompat for automatic UAC elevation. Retrieved from Bleen. All the integers between 6 and 7: http://lupwa.org/bleen/2015/02/08/upatre-downloader-malware-using-appcompat-for-automatic-uac-elevation/
- Bospoort, M. v. (2009, 7 23). Disabling a Shim. Retrieved from Maarten's blog: http://blogs.msdn.com/b/maartenb/archive/2009/07/24/disabling-a-shim.aspx
- Chen, R. (2005, 8 24). Buying an entire Egghead Software store. Retrieved from The Old New Thing - MSDN Blogs: http://blogs.msdn.com/b/oldnewthing/archive/2005/08/24/455557.aspx
- Cherepanov, A. (2014). Roaming tiger. Zeronights 2014 (p. 20). Moscow: http://2014.zeronights.org/assets/files/slides/roaming_tiger_zeronights_2014.pdf.
- Cherepanov, R. L. (2014, 1 25). Last-minute paper: Back in BlackEnergy: 2014 targeted attacks in the Ukraine and Poland. Retrieved from Virus Bulletin: https://www.virusbtn.com/conference/vb2014/abstracts/LM3-LipovskyCherepanov.xml
- Dr. WEB. (2014, 4 9). Retrieved from BackDoor.Gootkit.112—a new multi-purpose backdoor: https://news.drweb.com/show/?i=4338&lng=en
- Drapeau, P. (2015, 1 16). Firewall Rule Changes and Compatibility Trickery. Retrieved from Kill Chain. The Confer Blog: http://www.confer.net/kill-chain-the-confer-blog/80-firewall-rule-changes-and-compatibility-trickery
- Erickson, J. (2014). Persist It: Using and Abusing Microsoft Fix It Patches. BlackHat Asia, (p. 14). Singapore.
- F-Secure. (2015). BLACKENERGY & QUEDAGH. Retrieved from f-secure.com: https://www.f-secure.com/documents/996508/1030745/blackenergy_whitepaper.pdf
- Graham, C. (2014, 5 27). Shimming Your Way Past UAC. Retrieved from Digital Defense Incorporated: http://blog.ddifrontline.com/4#more-4
- Haruyama, T. (2015, 2 26). Github. Retrieved from TakahiroHaruyama / openioc_scan: https://github.com/TakahiroHaruyama/openioc_scan/blob/master/IOCs/generic/cdcd5fdb-fcd3-4947-8c76-d2fbdc1b5f82_UAC_COM.ioc
- Inocencio, R. (2014, 11 5). Banking Trojan DRIDEX Uses Macros for Infection. Retrieved from Security Intelligence Blog: http://blog.trendmicro.com/trendlabs-security-intelligence/banking-trojan-dridex-uses-macros-for-infection/
- msft-mmpc. (2013, 10 31). Upatre: Emerging Up(d)at(er) in the wild. Retrieved from Microsoft Malware Protect Center: http://blogs.technet.com/b/mmpc/archive/2013/10/31/upatre-emerging-up-d-at-er-in-the-wild.aspx
- Ollie. (2012, 4 28). Windows AppCompat Research Notes - Part 1. Retrieved from Research, Develop, Assess, Consult & Educate: http://recxltd.blogspot.co.uk/2012/04/windows-appcompat-research-notes-part-1.html
- Pernet, C. (2015, 3 30). Fake Judicial Spam Leads to Backdoor with Fake Certificate Authority. Retrieved from TrendLabs Security Intelligence Blog: http://blog.trendmicro.com/trendlabs-security-intelligence/fake-judicial-spam-leads-to-backdoor-with-fake-certificate-authority/
- Stewart, H. (2007, 11 3). Shim Database to XML. Retrieved from Setup & Install by Heath Stewart: http://blogs.msdn.com/b/heaths/archive/2007/11/02/sdb2xml.aspx
- Baggett, M. (2013, February 23). 2013 Posts and Publications. Retrieved October 23, 2013, from In Depth Defense: http://www.indepthdefense.com/2013/02/2013-posts-and-publications.html
- Ionescu, A. (2007, May 20). Secrets of the Application Compatilibity Database (SDB) – Part 1. Retrieved April 15, 2015, from Alex Ionescu's Blog: http://www.alex-ionescu.com/?p=39
- Ionescu, A. (2007, May 21). Secrets of the Application Compatilibity Database (SDB) – Part 2. Retrieved April 15, 2015, from Alex Ionescu's Blog: http://www.alex-ionescu.com/?p=40
- Ionescu, A. (2007, May 26). Secrets of the Application Compatilibity Database (SDB) – Part 3. Retrieved April 15, 2015, from Alex Ionescu’s Blog: http://www.alex-ionescu.com/?p=41
- Mark Russinovich, B. C. (2013, August 1). Autoruns for Windows v11.70. Retrieved September 5, 2013, from Windows Sysinternals: http://technet.microsoft.com/en-us/sysinternals/bb963902.aspx
- Microsoft. (2013, September 6). !chkimg. Retrieved October 2, 2013, from Dev Center: http://msdn.microsoft.com/en-us/library/windows/hardware/ff562217%28v=vs.85%29.aspx
- Microsoft. (2013, October 1). Application Compatibility Database. Retrieved October 23, 2013, from Microsoft Developer Network:http://msdn.microsoft.com/library/bb432182.aspx
- Microsoft. (2013). Fix it Solution Center. Retrieved 2013 24-October from Microsoft Support: http://support.microsoft.com/fixit/
- Microsoft. (2012, October 1). Microsoft Security Advisory: Vulnerability in Microsoft XML Core Services could allow remote code execution. Retrieved September 5, 2013, from Microsoft Support: http://support.microsoft.com/kb/2719615
- Microsoft. (2012, December 7). Shim Database Types. Retrieved September 5, 2013, from Microsoft Developer Network: http://msdn.microsoft.com/en-us/library/bb432483%28v=vs.85%29.aspx
- Sikka, N. (2013, September 17). CVE-2013-3893: Fix it workaround available. Retrieved October 02, 2013, from Security Research & Defense:
- http://blogs.technet.com/b/srd/archive/2013/09/17/cve-2013-3893-fix-it-workaround-available.aspx
- Stewart, H. (2007, November 3). Shim Database to XML. Retrieved September 5, 2013, from Setup & Install by Heath Stewart: http://blogs.msdn.com/b/heaths/archive/2007/11/02/sdb2xml.aspx